Intro — scope and purpose: This timeline surveys claims about “Crypto Exchange Proof-of-Reserves” by tracing key dates, public documents, and turning points in the debate about whether exchanges can (and have) proven their holdings. We treat the phrase “Crypto Exchange Proof-of-Reserves” as a claim: that exchanges have provided verifiable, comprehensive evidence of assets matching customer liabilities. The aim is to document primary sources, contemporaneous reporting, and technical literature so readers can see where the claim is documented, where it is disputed, and where gaps remain.
Timeline: key dates and turning points — Crypto Exchange Proof-of-Reserves
- 2011: Mt. Gox demonstrative transaction after scrutiny — event: In mid-2011 Mt. Gox moved a large block of BTC (often cited as the “424,242 BTC” transfer) as a public demonstration to address customer concerns. Source type: contemporaneous ledger evidence and community reporting; significance: early example of an on-chain “show” of control but one that leaked operational details and was never a repeatable audit method.
- 2014 (Feb–Aug): Early post‑MtGox push for solvency attestation — event: Several exchanges (Kraken, Bitstamp, Coinfloor, Huobi and others) published early proof-of-reserves or proof-of-solvency attestations and third‑party statements in 2014; Kraken used a Merkle-style approach and Coinfloor published iterative reports. Source type: exchange posts, contemporaneous press and community timelines. These early efforts established Merkle trees and third-party attestations as working models but were unevenly adopted.
- 2015: Academic cryptography proposals — event: Researchers published Provisions, a privacy‑preserving proof‑of‑solvency protocol that shows how an exchange could cryptographically prove assets ≥ liabilities without revealing sensitive customer or asset totals. Source type: peer‑reviewed computer‑security research. Significance: showed feasible cryptographic alternatives to simple asset-only proofs and underlined technical limitations of naive PoR approaches.
- 2016–2019: Ongoing technical work and limited deployment — event: Academic and engineering work (e.g., zkLedger, other proposals) explored privacy-preserving and zero‑knowledge approaches; but few exchanges adopted fully privacy-preserving proof-of-solvency in production. Source type: technical papers and industry commentary. Significance: the literature matured, but deployment lagged.
- November 2022: FTX collapse catalyzes new public push for PoR — event: After the sudden collapse of FTX in early November 2022, major exchanges publicly promised or published Merkle‑tree/asset proofs and wallet lists to reassure customers. Binance’s CEO encouraged Merkle‑tree proofs and Binance and other platforms published partial proofs for selected assets. Source type: news reporting and exchange announcements; significance: FTX’s failure turned PoR from a niche technical idea into an industry demand.
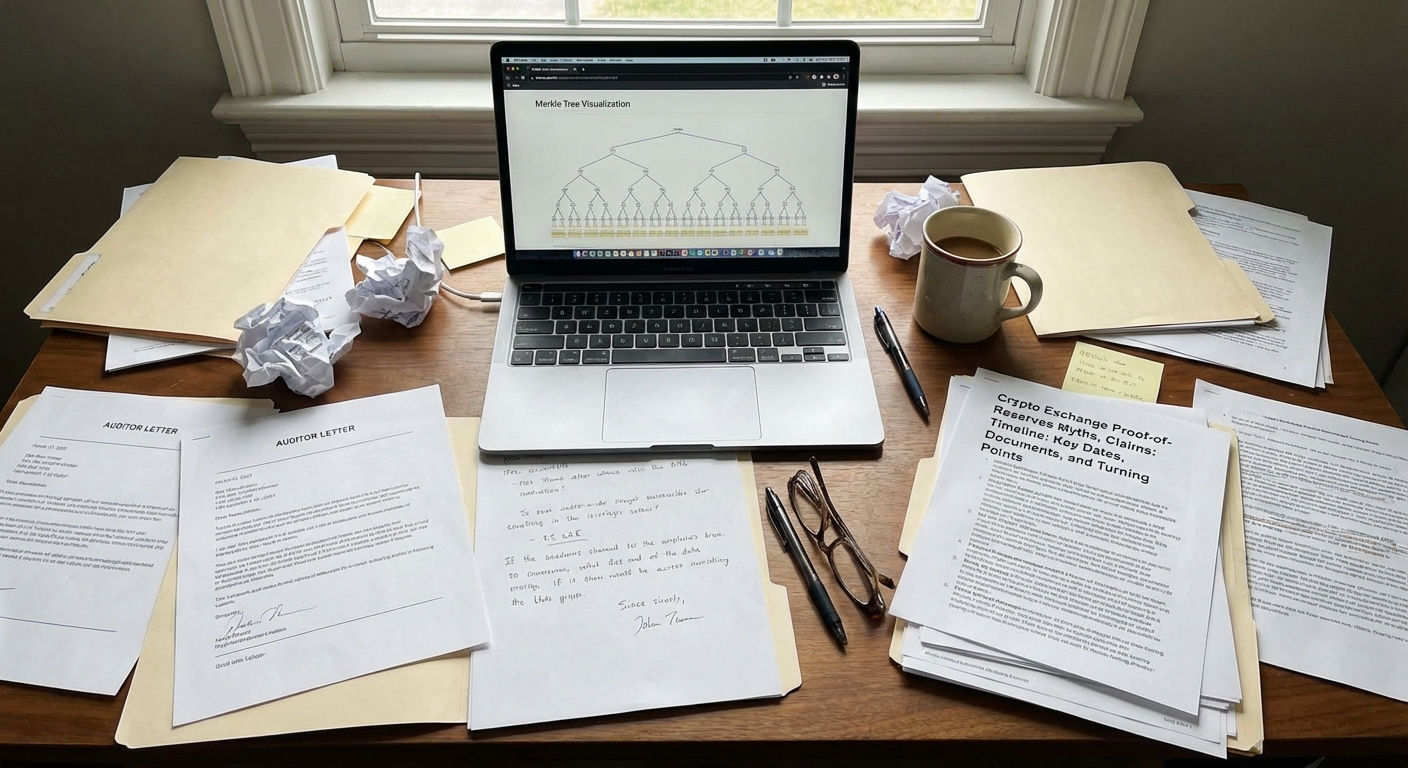
- Late Nov–Dec 2022: Merkle‑tree adoptions, third‑party letters, and rapid criticism — event: Several exchanges published Merkle‑tree snapshots or wallet lists; some used third‑party accounting letters (e.g., Mazars) to state holdings for selected assets. Critics quickly noted these attestations often covered only specific chains/assets, did not prove liabilities, and in many cases were not full audits. Source type: press coverage, exchange sites, auditor letters.
- December 16, 2022: Mazars suspends proof-of-reserves work and removes reports — event: Global accounting firm Mazars announced it would pause proof‑of‑reserves work for crypto clients and removed related pages after issuing reports for multiple exchanges; the firm said PoR reports were often misunderstood and did not provide sufficient assurance to the market. Source type: reporting quoting Mazars and firm statements; significance: a major auditor publicly stepping back showed limits in market trust and in the commercial auditing model for PoR.
- 2023–2024: Commercial PoR products, oracle integrations, and renewed critique — event: Firms and analytics providers (Merkle Science, Chainlink, SilverSixpence implementations) offered PoR tooling, oracles, or Merkle‑tree hosting, while analysts and journalists continued to document that many PoR feeds only guarantee data passage, not correct source accounting nor coverage of liabilities. Source type: vendor documentation and critical journalism. Significance: tooling improved, but critiques emphasized the difference between proving “data published equals data signed” versus proving complete solvency.
- 2024–2026: Ongoing evolution and mixed adoption — event: Exchanges continue to offer various PoR products (some expanded to more chains/coins or added liability trees), auditors and researchers continued to push for combined asset+liability methods or regulatory mandates in some jurisdictions. Source type: exchange documentation, industry reporting and academic proposals. The debate remains active: PoR practices differ by exchange and by the depth of third‑party assurance.
Where the timeline gets disputed
Several elements of the timeline and their interpretation are actively disputed by different parties. Key disputes include:
- Scope: whether a published Merkle root or wallet list constitutes a complete proof — some exchanges and vendors treated such publications as meaningful transparency steps, while critics noted they often cover limited assets or exclude liabilities (debate illustrated after November 2022).
- Assurance level: whether auditor letters from accounting firms equal formal assurance or an audit opinion — auditors like Mazars explicitly disclaimed that some PoR letters were not full audits and later paused the service, which observers read as evidence the market misinterpreted those letters.
- Technical completeness: whether Merkle‑tree proofs are vulnerable to manipulations of liabilities, off‑chain accounting, or temporary asset shuffling — cryptographers proposed stronger schemes (Provisions, zkLedger) but adoption and operational procedures (key‑usage, HSM access, scheduling) create practical gaps that can be exploited or misunderstood.
- Public interpretation: whether users understood PoR limitations — journalists and auditors documented widespread public confusion: many readers assumed a simple PoR proves full solvency, which technical authors and auditors warned was not necessarily true.
Evidence score (and what it means)
- Evidence score: 58/100
- Drivers: documented on‑chain wallet listings and Merkle roots exist for many exchanges (high-quality primary evidence for specific asset snapshots); peer‑reviewed cryptographic protocols (Provisions, zkLedger) show stronger technical designs are possible; major auditor statements and industry reporting show both adoption attempts and public misunderstandings; however, there is inconsistent coverage of liabilities, inconsistent auditor assurance, and documented retractions or suspensions (e.g., Mazars), which lower overall documentation strength.
- Documentation gaps: lack of consistently applied, auditor‑issued, full proof‑of‑solvency reports (assets + liabilities) across major exchanges; operational procedures that would prevent temporary manipulation are rarely public and rarely independently tested in production.
- Conflicts: primary sources sometimes conflict about scope (what an exchange’s Merkle snapshot covered), and major auditing vendors have changed positions — both reduce clarity.
Evidence score is not probability: The score reflects how strong the documentation is, not how likely the claim is to be true.
This article is for informational and analytical purposes and does not constitute legal, medical, investment, or purchasing advice.
FAQ
Q: What exactly is meant by “Crypto Exchange Proof-of-Reserves”?
A: The claim “Crypto Exchange Proof-of-Reserves” typically refers to assertions that an exchange has publicly verifiable evidence (often on‑chain addresses, Merkle‑tree roots, or auditor letters) showing that the exchange controls assets equal to customer deposits. The technical and audit methods vary; some proofs show only assets on certain chains or at a point in time, while others attempt to give user‑level inclusion proofs. Readers should note that “proof of reserves” as published by an exchange is not necessarily a proof of total solvency unless it is explicitly paired with independently verified proof of liabilities.
Q: Did the FTX collapse in November 2022 prove that PoR would have prevented the problem?
A: FTX’s failure highlighted why many market participants demanded more transparency, and it motivated exchanges to publish PoR artifacts. However, most critiques after the collapse argued that naive PoR (asset lists or single‑asset Merkle snapshots) would not have exposed all balance‑sheet exposures or related‑party liabilities that contributed to FTX’s insolvency. In short: FTX made PoR more urgent, but it did not prove that all forms of PoR would have prevented the collapse.
Q: Are Merkle trees sufficient to prove an exchange is solvent?
A: Merkle trees let users verify that their individual balance was included in a published snapshot without leaking other users’ balances. They can demonstrate that specific on‑chain addresses held a stated amount at a given block height. But they do not by themselves prove that (a) all liabilities were included correctly, (b) off‑chain accounting wasn’t manipulated, or (c) temporary asset borrowing wasn’t used to pass a snapshot. Cryptographic proofs that include liabilities exist in academic work (e.g., Provisions), but practical operational constraints and auditor involvement remain necessary for real‑world confidence.
Q: Can auditors provide full assurance for PoR?
A: Traditional audit firms can provide varying levels of assurance, but several firms have cautioned that short-form PoR letters are not equivalent to a full financial statement audit. In December 2022, at least one global firm paused or re‑scoped its engagements after concluding that public PoR products were frequently misunderstood and did not offer sufficient assurance in their current form. That episode underscores why many observers call for clearer standards and for asset+liability proof protocols or formal audits.
Q: What would change the assessment in this timeline?
A: The assessment would change if exchanges consistently published contemporaneous, auditor‑assured proof‑of‑solvency reports that (1) cryptographically or auditorily link on‑chain assets to exchange custody, (2) independently verify total liabilities (user balances) in a privacy‑preserving, verifiable manner, and (3) document robust operational controls that rule out temporary asset shuffling prior to a snapshot. Adoption of standardized, regulator‑mandated reporting formats or independent technical implementations of Provisions/zkLedger would materially strengthen documentation. citeturn3search0turn3search3
Beginner-guide writer who builds the site’s toolkit: how to fact-check, spot scams, and read sources.