Below are the arguments people cite in support of the claim that data brokers and large platforms maintain “shadow profiles.” These are presented as arguments supporters use, not as proven facts. The term “data brokers shadow profiles” appears throughout because it is the search‑style phrase used by researchers, reporters, and regulators when investigating the claim. For background and academic tests of the idea that social networks can infer information about non‑users, see peer‑reviewed studies and follow‑up reporting cited below.
The strongest arguments people cite
-
Argument: Platforms collect contact lists, device identifiers, and other inputs that allow them to assemble profiles of non‑users (often labeled “shadow profiles”).
Source type: Company feature behavior and public congressional testimony; investigative reporting.
How supporters verify or test it: Examine product features that request contact syncing or access to address books; review company testimony and transcripts from congressional hearings where executives were asked about profiles on non‑users.
Notes & evidence: Tech reporting and hearing transcripts have documented questions about collection of non‑user data and company denials/clarifications; for example, questions about Facebook’s collection of contact data and the term “shadow profiles” appear in coverage of executive testimony. Journalistic accounts cite both product behavior (contact syncing) and related disclosures when explaining this argument.
-
Argument: Cross‑site tracking, third‑party cookies, and browser fingerprinting create a dataset that can be linked to offline identifiers and sold or used by data brokers to enrich profiles of people who never signed up for a service.
Source type: Academic measurements of web tracking and industry analyses of tracking ecosystems.
How supporters verify or test it: Technical audits (network captures, tracker lists, and cookie/fingerprint scans), analysis of data broker catalogs, and controlled experiments that show linking between browsing signals and identity attributes.
Notes & evidence: Peer‑reviewed and preprint research quantify how platforms and tracking networks can follow both users and non‑users across the web; these studies show that browsing activity can be associated with demographic attributes and advertising identifiers that brokers and platforms use. The academic literature shows the technical plausibility of constructing inferred profiles from tracking signals.
-
Argument: Data brokers aggregate consumer records (purchase histories, public records, location data) and combine them with purchased lists; this aggregation can create detailed dossiers that include people who never consented to a particular profile.
Source type: Regulatory filings, government rulemaking proposals, and investigative reporting about the data broker industry.
How supporters verify or test it: Review broker product catalogs and sample data offerings, request subject access or opt‑out where available, examine regulatory findings or proposed rules that name brokers and specific practices.
Notes & evidence: U.S. regulators have recently targeted data‑broker practices; the Consumer Financial Protection Bureau proposed a rule in December 2024 aimed at limiting brokers’ sale of sensitive identifiers and clarifying when a seller functions as a consumer reporting agency. That regulatory work supports the argument that brokers collect and trade detailed personal data that can be used to build third‑party profiles.
-
Argument: Historical data leaks and breaches reveal that companies sometimes held data not explicitly provided by the account holder—interpreted by some as evidence of shadow profiles.
Source type: Breach reports and investigative journalism from earlier incidents.
How supporters verify or test it: Inspect breach disclosures, forensic reports, and follow‑up audits that list the types of data exposed and how the data was obtained (user‑submitted vs. inferred or provided by others).
Notes & evidence: Reporting around several high‑profile breaches and platform disclosures has been used to argue that companies had collected information beyond what users directly supplied; journalists and researchers cite those disclosures when describing the origins of the “shadow profile” idea.
-
Argument: Predictive models can infer sensitive attributes (for instance, sexual orientation or political leaning) from network and behavioral data, creating effective “shadow” inferences without explicit user input.
Source type: Peer‑reviewed research and public demonstrations by academic teams.
How supporters verify or test it: Replicate model training on open datasets (where allowed), evaluate accuracy and error rates, and inspect whether models require user‑provided labels or can generalize from neighbors’ information.
Notes & evidence: Academic studies have demonstrated that social network topology and disclosure by others can enable prediction of attributes for non‑users or unlabelled accounts; these studies are often cited to show that building inferred profiles is technically feasible.
Data brokers shadow profiles — How these arguments change when checked
When each argument is tested, the results fall into three recurring outcomes: (1) documented operational practices or measurements that support the mechanism claimed; (2) technically plausible inference or aggregation that is demonstrable in academic settings but not always proven at scale for named companies; and (3) gaps in the public record where the alleged practice is plausible but not directly evidenced in publicly available documents. Below we walk through how the strongest arguments typically hold up when scrutinized.
-
Contact syncing and non‑user records: Platforms’ contact‑sync features are documented; congressional questions and reporting have shown companies collect contact lists and sometimes use them for security or recommendation features. That validates the mechanism that user contacts can seed information about non‑users. However, whether a specific company packages those inputs into a persistent, queryable “shadow profile” sold or shared in the same way a broker sells data is less often documented publicly. Supporters’ inference is plausible and partially documented, but the precise commercial uses and retention policies vary and are not always available in public records.
-
Tracking and inference at internet scale: Technical studies show trackers and platforms can follow users and non‑users across sites, and models can infer attributes from patterns. Academic work quantifies the potential to reconstruct attributes, which supports the claim’s technical plausibility. Still, proving that named data brokers or companies operationalize these exact models into durable, identifiable shadow profiles (as opposed to ephemeral targeting identifiers) requires access to internal logs, vendor contracts, or regulatory disclosures that are often unavailable.
-
Data broker aggregation: Regulators and investigations have long documented that the broker industry aggregates consumer records from many sources. This supports the argument that brokers can assemble comprehensive dossiers. Yet whether those dossiers match the precise image many critics paint (a single, unified “shadow” identity used across multiple services) depends on broker practices, contractual constraints, and how companies map identifiers—details that are sometimes proprietary or redacted in disclosure. The CFPB’s proposal to classify some activities as consumer reporting highlights regulatory concern but does not by itself confirm every allegation made about shadow profiling.
-
Breaches and exposed data: Breach reports show that companies sometimes held data not directly supplied by account holders, which is consistent with the notion that platforms collect third‑party data. However, breach evidence proves only that data existed in a given system at a given time; it does not always prove how that data was assembled, how persistently it was stored as a standalone “profile,” or whether it was used commercially.
This section intentionally separates (a) the technical mechanisms that make shadow‑profile‑style inference possible, (b) documented examples where related data exists in corporate systems, and (c) the more expansive claims that a single company or the broker industry always produces, maintains, and monetizes comprehensive shadow dossiers on all non‑users—claims that are often asserted but not fully demonstrated in public records. Where sources conflict, public records and peer‑reviewed studies should be prioritized; in many cases they corroborate the mechanism but not the commercial scale claimed by advocates.
This article is for informational and analytical purposes and does not constitute legal, medical, investment, or purchasing advice.
Evidence score (and what it means)
- Evidence score: 58 / 100
- Drivers that raise the score:
- Multiple peer‑reviewed studies and preprints show the technical feasibility of inferring attributes from contacts and browsing signals.
- Regulatory action and proposed rules confirm that the data broker industry collects and trades detailed personal data.
- Investigative reporting and congressional questioning document collection behaviors (e.g., contact syncing) that can produce non‑user records.
- Drivers that limit the score:
- There is limited direct public evidence showing continuous, unified “shadow profiles” branded or sold exactly as the claim implies; many details remain proprietary or unpublished.
- Academic tests are often model demonstrations or audits on available datasets; they prove feasibility but not necessarily company‑scale deployment.
Evidence score is not probability:
The score reflects how strong the documentation is, not how likely the claim is to be true.
FAQ
What exactly do people mean by “data brokers shadow profiles”?
Supporters use the phrase to refer to compiled dossiers—often claimed to include people who never signed up with a service—assembled by brokers or platforms using contact lists, tracking signals, public records, and purchased data. Researchers use similar language for inferred attributes that platforms can predict about non‑users. The term mixes technical mechanisms (tracking and inference), commercial practices (broker aggregation), and normative concerns (consent and control).
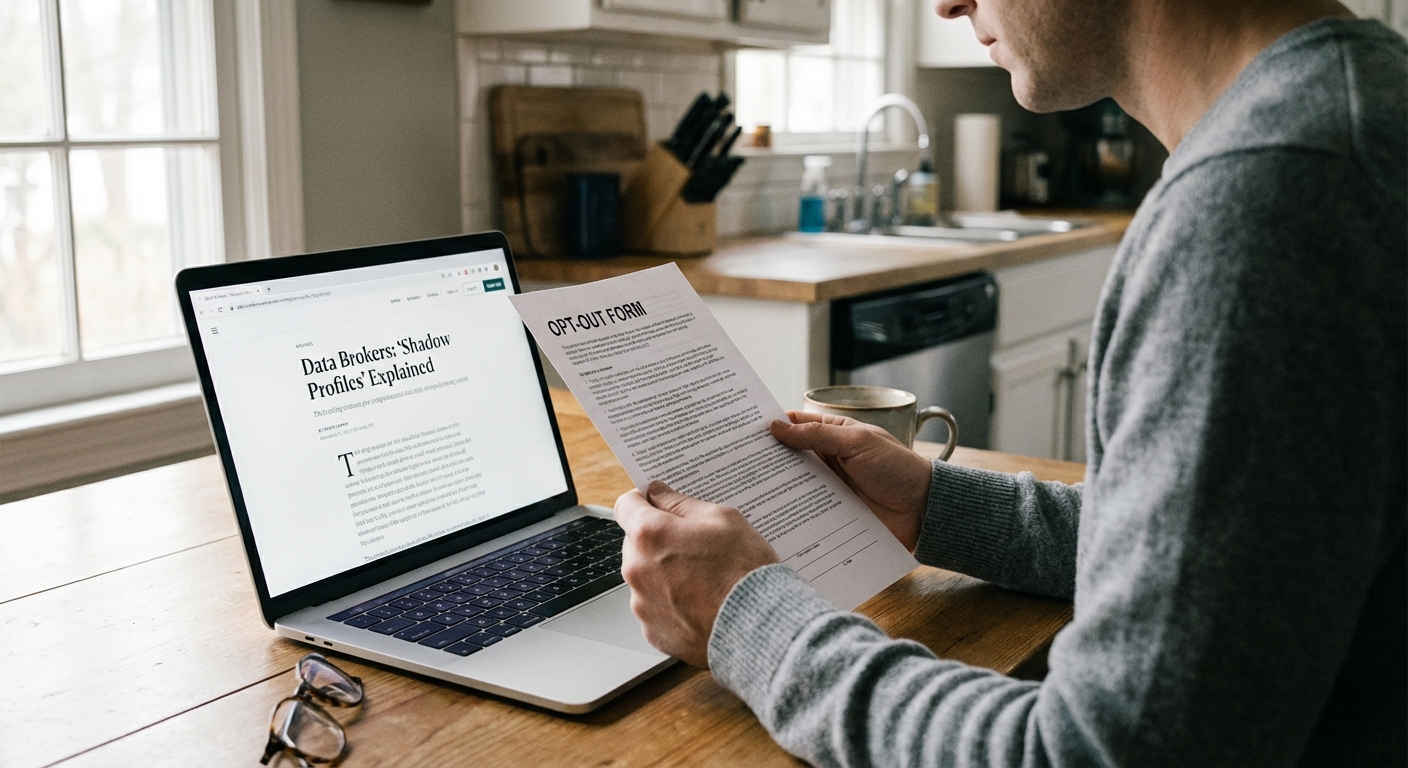
How can I check if a data broker has information about me?
You can attempt subject‑access procedures or opt‑out pages that many major brokers provide, though completeness and responsiveness vary by provider and jurisdiction. Regulators and consumer advocates maintain lists of broker opt‑out URLs and guidance; testing those channels is the practical verification step for individuals. The CFPB and other agencies are actively reviewing whether stronger access and accuracy rules should apply.
Are there peer‑reviewed studies that show shadow profiles are possible?
Yes. Multiple academic studies have demonstrated that information disclosed by users and the structure of social networks can enable accurate inference of attributes for others in the network; these works show technical feasibility but do not alone prove that any particular company creates and sells a unified “shadow profile” product. See, for example, a 2017 Science Advances study and follow‑up network audits.
Does regulation already ban shadow profiling?
U.S. federal regulators have increased scrutiny of data brokers and proposed rules to limit sale of sensitive identifiers and to apply consumer‑reporting rules in some cases, but there is not yet a uniform federal ban on inferred profiles; rules vary by jurisdiction and are evolving. The CFPB’s December 2024 proposal is an active regulatory step but not a finalized prohibition.
How reliable are the strongest arguments people cite?
The strongest arguments are backed by documented mechanisms (contact syncing, tracking, broker aggregation) and peer‑reviewed demonstrations of technical inference. They are reliable to the extent they show plausibility and known practices. They are less reliable when claims move from “this is technically possible” to “this exact, persistent, monetized shadow profile exists for every person,” which requires additional, company‑specific evidence often absent from public records.
Tech & privacy writer: surveillance facts, data brokers, and what’s documented vs assumed.